APRIL 27TH, 2015
By ADMIN
To enable external SSH access to a brand new Cisco ASA 5512-X, follow these example instructions:
X.X.X.X is the IP address you wish to allow access from.
yourusername is the username you want to use
XXXXXXXXXXXXXXXXX is your password
ciscoasa# conf t
ciscoasa(config)# ssh X.X.X.X 255.255.255.255 outside
ciscoasa(config)# crypto key generate rsa general-keys modulus 2048
ciscoasa(config)# username yourusername password XXXXXXXXXXXXXXXXX
ciscoasa(config)# aaa authentication ssh console LOCAL
ciscoasa(config)# ssh version 2
You may also want to set an enable password:
ciscoasa(config)# enable password XXXXXXXXXXXXXXXXX
(You should probably make this different to your user password)
JANUARY 29TH, 2015
By ADMIN
For those that missed it, CVE-2015-0235 (aka Linux Ghost) was announced today which details a glibc library bug that is still on many Linux distributions. glibc is used by many applications including webservers, mail servers, php applications etc.
The specific bug was in the gethostbyname() and gethostbyname2() functions (hence “ghost” name!), so only applications that call these are potentially vulnerable. Even then, there is limited scope for exploitation, but there already has been a PoC for the Exim mail server developed so it certainly is possible (given the right conditions). Luckily, these two functions lack IPv6 support, so many newer applications and services have chosen to stop using these functions, and instead use IPv6-enabled functions instead. As has been seen however, some popular ones such as Exim do still use the older IPv4-only functions.
The bug itself has been around since 2000, and was inadvertently patched in August 2014 without realising the implications. Unfortunately since the security issues were not detected at the time, many Linux distributions didn’t back-port the patch into Linux distributions. This is what has occurred today.
Accordingly, we have now taken the following actions:
All standard-level webservers globally and chroot environments have been patched and restarted between 6:30AM and 7:15AM this morning.
All mail servers were patched and restarted between 6:30AM and 7:15AM this morning.
We will be taking the following actions that may result in a few minutes downtime for some sites tonight:
All protected-level webservers globally and chroot environments will be patched and restarted overnight at varying times (critical maintenance alert will have been received by all affected customers). As these are all behind load balancers, this shouldn’t have any end-user affect.
RackCorp monitoring services will be restarted throughout the day. This may result in some performance graphs being slightly skewed at times.
In addition:
VM Hosts will have no noticeable impact.
Load Balancer services will have no noticeable impact.
RackCorp API services will have no noticeable impact (however some unrelated database maintenance is scheduled for tonight that may result in queries taking a few seconds longer than usual).
Content delivery services are unaffected.
Network services are unaffected.
In terms of customer patch cycles, we are treating this as a critical bug for some customers, and moderate (normal patch cycle) for others depending upon the attack vector surface area. All affected customers will have received an email accordingly. If you are unsure of the impact for your specific services, please raise a support ticket accordingly.
Additional useful resources:
Ars Technica Writeup on Linux Ghost
gethostbyname() vs getaddrinfo() by Erratasec
It would seem that it’s rather difficult (not possible?) to deactivate the ISL exchange between Brocade switches. This normally isn’t a problem unless you really want to segment your Brocade switches by not running ISL trunking between certain ones. As soon as you want to do this you may come across your interface in this state:
line protocol down (ISL DOWN)
Points you in the direction of ISL but when you’ve explicitly disabled fabric ISL for the interface:
no fabric isl
no fabric trunk
You may be left wondering how to disable it. We tried a few things but the Brocade ISL seems to operate at a lower level than the commands presented in NOS. Anyway the eventual solution was simply to change the vcs ID:
vcs vcsid XXX
Where XXX is different to your other switches.
It’s probably the cleaner solution in any case. Had we set things up properly in the lab in the first place then we wouldn’t have encountered this issue at all, but then again we now have the knowledge that NOS is doing things behind the scenes at a lower level than we’ve really got access to (when vcs mode is enabled). I guess it’s always nice to discover this in a lab environment first anyway.
Our first production deployment of Brocade VDX6740 & VDX6710 switches will be occurring later this week in Perth Australia. We’re really enjoying the multi-chassis LACP within a vcs fabric feature (I’m not sure any other switching fabrics support this?). It gives us an opportunity to do some fancy redundancy deployments – at least that’s how it’s working in the lab – watch this space for some real world experience coming up soon!
We are pleased to announce high-availability premium virtual servers via in Metronode’s recently completed Melbourne 2 Data Centre located in Victoria, Australia.
This data centre is unique in that not only does it allow us to offer hosting and server products in a location geographically convenient to Southern Australian users, but provides very high security and energy efficiency features.
Our Melbourne point of presence is ideal for customers in Victoria, South Australia and especially Tasmania who are seeking the best latency and speeds to their websites.

RackCorp’s in-house developed management system and global network
Combined with Metronode’s Tier 3 Rating means our Melbourne site is ideal for customers who require a higher level of redundancy and reliability
What Exactly is a Tier 3 rating?
A specification defined by both the Uptime institute and ANSI/TIA of USA which contains formal requirements for the design of a data centre.

The rating covers items such as
- Site space and layout
- Physical infrastructure such as cabling, site security, access control and power.
- Reliability rating of the sites infrastructure
- Environmental efficiency and Management, both internal and external
Very few data centres in Australia are Tier 3 rated as a number are just designed to best-practise rather than an industry recognised specification.
Energy Efficiency – the future key to reliable web hosting
A commonly cited metric to measure a data centre is its PUE (power utilization efficiency) rating. The lower the PUE, the more efficient the cooling, better the reliability with less chance of outages and the lower the energy costs.
Metronode’s unique ‘BladeRoom’ data hall design and Melbourne’s cool climate enable a very low PUE of 1.1, one of the lowest possible and best in Australia.

One of the key principles behind our company is emphasis on in-house custom developed solutions based on open source software.
A bespoke open source foundation provides us with
- Maximum reliability as bugs can be patched before official fixes are available
- Maximum performance thanks to streamlined and lean code
- Maximum flexibility and extensibility to meet our customers and our own specific needs
- Minimising cost and licensing which helps keeps prices competitive
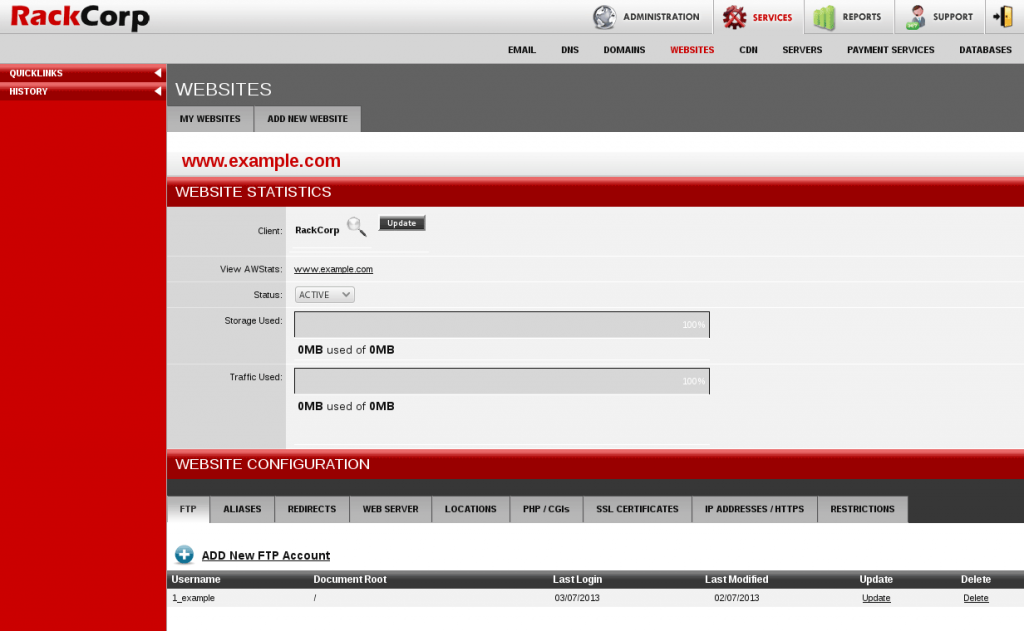
These principles form the basis on which is why we built RackAdmin, the backbone of our company since foundation. A custom, in house developed management platform which provides end-user account management, option and service provisioning including reseller management and geo-location and automated billing. All within a slick and easy to use interface and an API.
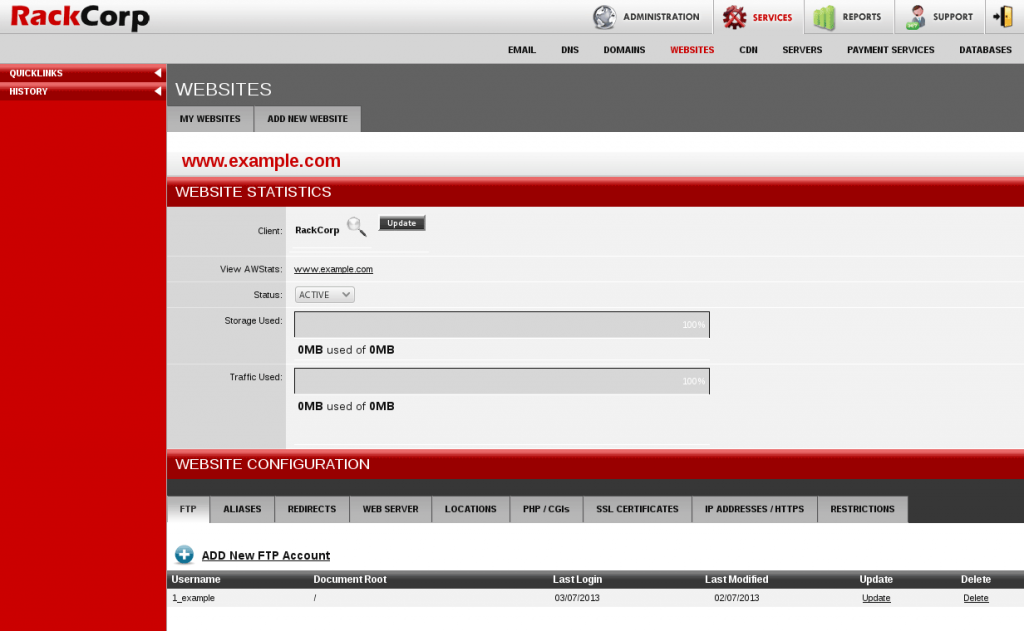
Rackadmin provides is a streamlined,slick and easy to use solution to manage your web hosting needs
Read more »